More than 25% of Scottish businesses have faced a cyber attack in the last three years, while the Scottish public sector has handled 183 cyber incidents since 2018, according to the Scottish Cyber Activity Report 2026. For founders, that isn't just an IT issue. It's a continuity issue, a customer trust issue, and very often a media issue.
When a breach, fraud event or major outage hits, most businesses don't struggle because they lack a policy document. They struggle because the problem moves faster than their decision-making. Systems fail, staff improvise, customers want answers, and journalists start asking questions before the internal facts are settled.
That's why the scottish business resilience centre matters. It sits in the practical space between prevention and response. Not abstract strategy. Not software for software's sake. Real-world support that helps Scottish organisations prepare for disruption before it turns into reputational damage.
From a communications perspective, that's the overlooked point. A resilient business doesn't just recover faster. It speaks more clearly, protects confidence better, and avoids the kind of confused public response that makes a bad incident worse.
Why Resilience is Your New Competitive Edge
A lot of businesses still treat resilience as a compliance line or an annual board paper. That's too narrow. Resilience now shapes whether customers trust you, whether suppliers keep backing you, and whether your team can function under pressure.

For Scottish SMEs, the commercial question isn't whether disruption is possible. It's whether your organisation can absorb it without losing momentum. The firms that handle incidents well usually aren't the biggest. They're the ones that have already decided who leads, what gets prioritised, and how they'll communicate when the pressure is on.
What resilience changes in practice
A resilient company can do four things quickly:
- Spot the issue early: Staff know what abnormal activity looks like and escalate it fast.
- Keep critical operations moving: Leadership understands which systems, suppliers and decisions matter first.
- Communicate with discipline: Customers, partners and staff hear a coherent message instead of guesswork.
- Protect brand value: The organisation avoids looking evasive, disorganised or technically out of its depth.
That last point matters more than many founders realise. In a crisis, people rarely separate operational competence from brand credibility. If your response looks slow or muddled, they assume your business is the same.
Strong resilience work reduces the gap between what your business can actually handle and what the public thinks it can handle.
Why the scottish business resilience centre stands out
The scottish business resilience centre has become central to this conversation because it isn't offering resilience as a buzzword. It helps businesses build practical readiness through assessment tools, training and awareness work that connects national threat knowledge to day-to-day business reality.
That makes it relevant beyond security teams. Founders need it because incidents threaten growth. Operations leads need it because disruption spreads across workflows. Communications leads need it because every operational failure has a public-facing consequence.
In Scotland, that joined-up view matters. Businesses operate in a close ecosystem where sector reputation travels fast. A cyber issue at one firm can quickly become a trust issue across a category, especially in professional services, tourism, hospitality and high-growth tech.
What is the Scottish Business Resilience Centre
The simplest way to think about the scottish business resilience centre is this. It's a publicly backed neighbourhood watch for the Scottish business community, but built for modern threats rather than just physical crime.
It was founded in 1996 and is headquartered in Linlithgow. It is a non-profit organisation established through a partnership between the Scottish Government, Police Scotland, and the Scottish Fire & Rescue Service, as outlined by the National Business Crime Centre partner profile. That structure gives it a level of authority and practical relevance that private providers often struggle to match.
Why its structure matters
Plenty of organisations sell cyber support. Fewer sit inside a framework that connects public bodies, policing insight and business engagement in the same place.
That matters for two reasons.
First, Scottish businesses don't need more noise. They need guidance that reflects the threat environment they face. Second, crises rarely stay inside one department. Fraud, cyber risk, physical security, continuity planning and communications often collide in the same week.
The useful test isn't whether advice sounds expert. It's whether it helps a business make better decisions under pressure.
The centre's model is designed around that practical reality. It isn't only there to explain risk. It's there to make organisations more prepared to handle it.
From crime prevention to cyber and fraud readiness
Its history also explains why the organisation still matters. The centre began life in a business crime context, focused more heavily on physical threats. That legacy is useful because many firms still face blended risks, where a fraud attempt, a data exposure and an operational disruption don't arrive as separate events.
As threats changed, the organisation evolved. Its rebrand to the Cyber and Fraud Centre – Scotland signalled a sharper focus on the risks that now hit Scottish SMEs most directly. That shift wasn't cosmetic. It reflected the fact that business resilience now lives as much in inboxes, cloud systems, payment processes and remote working habits as it does in locks, alarms and access control.
What it does better than a generic awareness campaign
A general awareness campaign can tell a founder to take cyber seriously. The scottish business resilience centre goes further by turning that concern into action.
A useful way to compare it is below:
| Approach | What it tends to do | What businesses actually need |
|---|---|---|
| Generic cyber messaging | Raises awareness | Clear next steps |
| One-off compliance activity | Ticks a requirement | Ongoing readiness |
| Purely technical support | Focuses on systems | Support for people, process and response |
| SBRC-style resilience model | Connects threat insight, training and continuity | Better decision-making during disruption |
For founders, the value isn't theoretical. It's access to a trusted framework that helps reduce uncertainty before a crisis lands on the desk.
Decoding SBRC Core Services for Your Business
Most businesses don't need another vague resilience promise. They need to know what the scottish business resilience centre helps them do on a difficult Monday morning.
The clearest way to break it down is by outcome. Not every service will matter equally to every company, but the centre's value tends to sit across four practical areas: cyber support, training, fraud awareness, and incident response readiness.
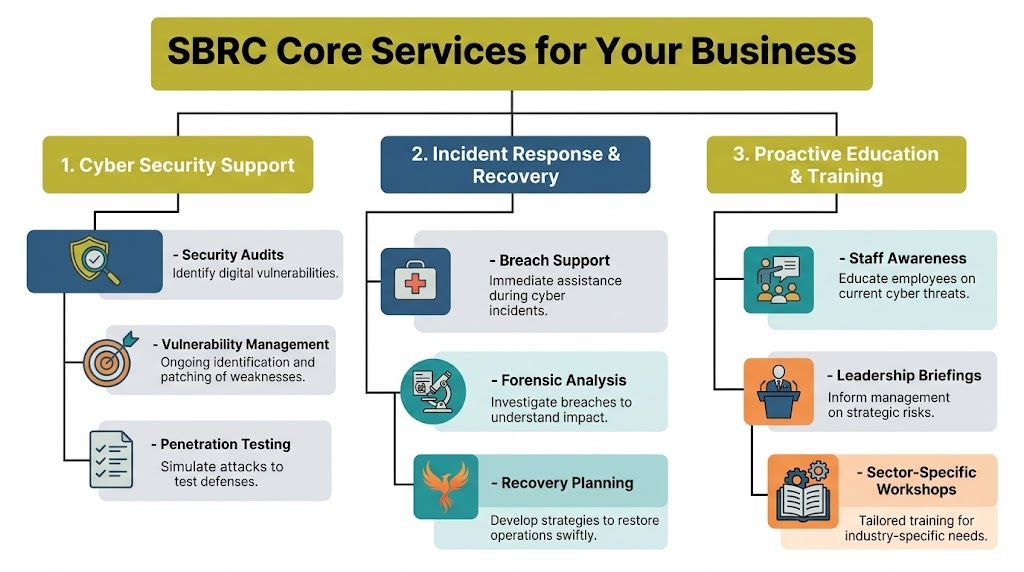
Cyber support that identifies weak points
Many SMEs know they have cyber risk. Fewer know where it sits in operational terms. The centre's cyber support is valuable because it helps translate a technical issue into a business issue.
That usually means pressure-testing where a company is exposed. Remote access, staff behaviours, supplier dependencies, outdated processes, and weak escalation routes all matter. A founder doesn't need to become a security analyst. They do need a clearer view of where one bad click or one avoidable gap could disrupt trading.
Operational rule: If leadership can't explain which digital failure would hurt the business most, it hasn't assessed risk clearly enough.
For communications teams, that clarity matters as well. If an incident happens, your external response is only as good as your internal understanding of what failed.
Training that builds muscle memory
For SMEs, the centre proves especially useful. Workshops such as Exercise in a Box work because they don't rely on passive learning. They simulate pressure. Teams rehearse decisions. Leaders see where assumptions break down.
According to Professional Security coverage of SBRC activity in Tayside, 'Exercise in a Box' and other cyber courses demonstrated a 35% enhancement in policy refinement for participating SMEs, with phishing detection improving from 15% to 55% in regional pilots. That's useful because policy quality often looks fine until someone has to use it under stress.
A tabletop session is often more revealing than a lengthy document review. Teams discover who owns decisions, where language is unclear, and whether the business can tell the difference between inconvenience and a genuine crisis. That's also why many businesses benefit from understanding what a specialist crisis management agency does once an issue moves into the public domain.
Fraud awareness that matches current threats
Fraud often gets treated as a finance problem. In reality, it sits across people, culture and process. A spoofed invoice, a fake executive request, or a social engineering attempt can trigger reputational fallout as quickly as a breach.
The centre's fraud-focused work helps businesses tighten the points where trust can be exploited. That's particularly important in founder-led firms where staff move quickly and informal approval habits are common. Speed helps growth, but it can also create weak controls.
Three areas usually need attention:
- Payment approval discipline: Staff need clear verification steps when money or account changes are involved.
- Senior leader impersonation: Teams should know that urgency is a common fraud tactic.
- Supplier communication checks: Procurement and finance processes need enough friction to stop avoidable mistakes.
Incident response readiness that supports continuity
The centre is also valuable before an incident because it improves how a company reacts during one. That's a different discipline from prevention. Good incident response depends on sequencing. Who decides first. What gets checked. Which stakeholders need notice. What can be said confidently, and what can't.
For SMEs, the most common mistake is trying to invent the response during the incident. The stronger approach is to pre-build the structure. Define roles, set thresholds, and rehearse likely scenarios.
A simple way to view the service mix is here:
| Service area | Business problem it helps solve | Practical benefit |
|---|---|---|
| Cyber support | Unknown technical and operational exposure | Better visibility of business risk |
| Training and simulations | Unpractised teams | Faster, calmer decisions |
| Fraud awareness | Process and people vulnerabilities | Fewer preventable errors |
| Incident readiness | Disorder during live disruption | Clearer internal and external response |
What works is repetition, realism and leadership involvement. What doesn't work is filing a plan and assuming that counts as preparedness.
Putting Resilience into Practice Real-World Scenarios
The best way to judge the scottish business resilience centre is to look at how its support fits real business situations. Not idealised ones. The messy, recognisable kind that founders and managers deal with every week.

A startup that has grown faster than its controls
A tech startup in Glasgow lands new clients quickly and expands its team. Processes stay informal because speed matters. The founder still approves key decisions personally. Security awareness exists in principle, but there hasn't been much structured testing.
Resilience work earns its keep in this context. A practical assessment gives the leadership team a map of operational dependencies, not just a list of abstract risks. For SMEs, that's important because the SBRC provides a Scotland-wide risk and business continuity assessment tool designed for SMEs, and evidence from its use shows it can lead to a 20-30% reduction in downtime through pre-emptive mitigation strategies, according to the Scottish Government FOI release on the tool.
For a startup, the gain isn't only technical. The team gets sharper on what must stay running if systems are interrupted, which clients would need early contact, and what internal approvals can no longer live inside one person's inbox.
A professional services firm facing a trust-sensitive incident
A regulated advisory firm doesn't need a catastrophic breach to suffer reputational harm. It only needs uncertainty. A suspicious email chain, a compromised account, or a payment-related scare can cause clients to question discretion and control.
Simulation helps. Exercises force senior people to practise their judgement before a live event. A lot of leadership teams discover they have technical playbooks but no agreed language for clients, staff or regulators.
Teams looking to improve rehearsal quality often benefit from reviewing how cyber resilience tabletop exercises are structured, especially when they want scenarios that test decisions rather than just policies.
A professional services firm also needs to align technical response with public response. If the legal team, IT provider and leadership team are all working from different assumptions, confidence erodes fast.
Later in the process, examples of external handling become just as important as internal containment. That's why it helps to study practical crisis communications examples before an incident forces you to improvise.
A short overview of resilience thinking in action is worth watching here:
A hospitality business where downtime hits publicly
A hotel group, visitor attraction or restaurant operator has a different risk profile. The pressure is immediate and visible. Booking systems fail, customer data concerns spread quickly, and frontline staff have to answer questions in real time.
In hospitality, resilience isn't hidden in the server room. Guests experience it at reception, on the website, and across review platforms.
For this type of business, continuity planning has to account for operational reality. Can bookings still be managed? Can the team brief guests consistently? Can the business explain the disruption without sounding defensive or vague?
What works is a joined-up approach. Risk assessment informs operations. Simulations expose decision gaps. Then communications planning turns those findings into usable holding lines, stakeholder messages and escalation routes.
What doesn't work is treating cyber and reputation as separate workstreams. Customers don't see it that way, and journalists won't either.
Engaging with the SBRC Membership and Partnership Options
The scottish business resilience centre becomes most useful when businesses stop treating resilience as something they'll get round to later. The right time to engage is before your team is under pressure, not during an active incident.
One reason the urgency has sharpened is the change in the threat picture itself. The centre's rebrand to the Cyber and Fraud Centre – Scotland was driven by a 92% rise in cyber-related crime and fraud in Scotland over the last two years, as reported by FutureScot's coverage of the rebrand. That shift tells you something important. Businesses aren't only defending against technical compromise. They're dealing with a broader mix of deception, social engineering and operational risk.
What engagement usually looks like
Not every business needs the same level of involvement. Some start with public-facing guidance and awareness activity. Others need a closer relationship because they operate in a regulated market, hold sensitive data, or have a board that wants stronger oversight.
In practice, engagement usually falls into three broad levels:
- Light-touch engagement: Useful for firms that need awareness, signposting and a clearer understanding of current threats.
- Structured participation: Better for SMEs that want training, scenario work or practical assessments tied to operations.
- Deeper partnership thinking: Most relevant when resilience needs to connect across leadership, compliance, IT, people and public response.
How to decide what fits
The right route depends less on company size and more on exposure. A small firm with sensitive client relationships may need more discipline than a larger business with limited public scrutiny.
A quick decision filter helps:
| If your business is dealing with… | You likely need… |
|---|---|
| Fast growth and informal processes | Structured training and review |
| High trust client relationships | Clear continuity and response planning |
| Frequent supplier or payment activity | Stronger fraud awareness controls |
| Public-facing service disruption risk | Joined-up incident and communications readiness |
Good engagement starts with honesty. If your current plan only works when everyone is calm and available, it isn't a crisis plan yet.
A straightforward way to get started
Most founders overcomplicate the first step. It doesn't need to be dramatic.
- Review your current exposure: Look at where customer trust, operational continuity and digital dependency intersect.
- Identify one realistic scenario: Choose the disruption most likely to test your business.
- Engage with practical support: Prioritise assessment, training or awareness work over generic reading.
- Bring leadership into the process: Resilience can't sit solely with IT or admin.
- Treat it as a capability, not a document: The aim is better response behaviour, not just better paperwork.
Businesses that do this early usually make faster and cleaner decisions later.
Your Next Steps A Resilience Action Plan
Resilience only becomes real when it's assigned, tested and reviewed. If responsibility sits everywhere, it sits nowhere. The practical move now is to separate what founders need to own from what communications leads need to prepare.

For founders and chief executives
Founders should treat resilience as part of business design, not just risk management. That means asking whether the company can still function if one key system, supplier, person or payment channel is disrupted.
Focus on these actions:
- Set ownership clearly: Name the senior person who leads continuity and the person who deputises.
- Define critical operations: List the services, systems and relationships the business can't afford to lose.
- Test one disruption scenario: Choose the event most likely to halt trading or damage confidence.
- Review external dependencies: Check which suppliers, platforms or outsourced partners create concentrated risk.
- Strengthen continuity planning: If you need a clear primer on why this matters, this guide to business continuity planning is a useful companion read.
A founder's job isn't to know every technical detail. It's to make sure the organisation has the structure, authority and discipline to respond well.
For communications leads and brand teams
Communications people often get pulled in too late, after an incident has already become visible. That's a mistake. Comms should be involved when scenarios are being tested, because reputation risk doesn't begin at the press statement stage.
Work through this checklist:
- Build holding statements early: Draft language for likely disruption scenarios before anyone needs approval at speed.
- Map stakeholder order: Decide who hears from you first, including staff, customers, partners and regulators where relevant.
- Pressure-test spokesperson readiness: Make sure senior leaders can explain what happened, what is being done, and what comes next.
- Align facts with tone: Accuracy matters, but so does sounding competent and human.
- Prepare recovery messaging: Stakeholders will want to know when operations are stable and what has changed.
The SBRC helps a business strengthen the digital fortress. Reputation planning protects the story outside its walls.
For organisations that want a stronger external framework around trust, scrutiny and media handling, reputation planning should sit alongside technical readiness. That's where specialist support on reputation management services in the UK becomes relevant.
What good looks like
A strong resilience posture is rarely dramatic. It looks organised. Leadership knows its role. Staff have rehearsed. Risk has been translated into plain language. Customers get timely information. The business doesn't hide, speculate or freeze.
That's the standard worth aiming for. Not perfection. Composure under pressure.
If your organisation needs senior support on the reputational side of resilience, Carlos Alba Media can help. We're a Scottish-led agency made up of former national news journalists and experienced agency professionals who have worked with international brands. That background matters when an operational issue becomes a public one. We help founders, leadership teams and communications leads prepare for scrutiny, manage live incidents, and protect trust when the story moves fast.